Insidious rat Cracked 2026
Short Intro:
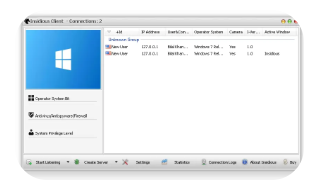
Insidious RAT Cracked 2026 is a pirated version of a premium Remote Access Trojan (RAT) circulating in hacker forums, offering unauthorized users full system control without licensing restrictions. This cracked variant retains the original malware’s powerful surveillance capabilities while adding custom obfuscation and evasion tweaks to bypass modern security solutions. Designed for stealthy, long-term access, it poses a severe risk to personal privacy, corporate networks, and financial security.
Features:
Invicta Stealer (2026-style variants) is a dangerous information-stealing malware, and its “features” are actually malicious capabilities used in cyberattacks. Below is a detailed breakdown of its advanced features in paragraph form (for cybersecurity awareness):
Invicta Stealer is designed for deep system reconnaissance and profiling, meaning it collects extensive information about the victim’s device, including OS version, username, hardware specs, IP address, geo-location, timezone, and running processes. This helps attackers understand the environment before exploiting it further.
Virus Total Scan Result:
Download Now
Short Intro:
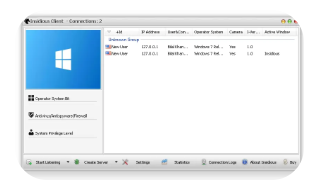
Insidious RAT Cracked 2026 is a pirated version of a premium Remote Access Trojan (RAT) circulating in hacker forums, offering unauthorized users full system control without licensing restrictions. This cracked variant retains the original malware’s powerful surveillance capabilities while adding custom obfuscation and evasion tweaks to bypass modern security solutions. Designed for stealthy, long-term access, it poses a severe risk to personal privacy, corporate networks, and financial security.
Features:
Invicta Stealer (2026-style variants) is a dangerous information-stealing malware, and its “features” are actually malicious capabilities used in cyberattacks. Below is a detailed breakdown of its advanced features in paragraph form (for cybersecurity awareness):
Invicta Stealer is designed for deep system reconnaissance and profiling, meaning it collects extensive information about the victim’s device, including OS version, username, hardware specs, IP address, geo-location, timezone, and running processes. This helps attackers understand the environment before exploiting it further.
Virus Total Scan Result:
Download Now





