leo_marshall63
Registered
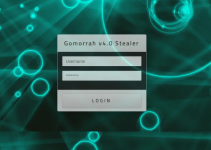
Gomorrah Stealer operates with a modular architecture that allows it to be highly adaptable and scalable, making it suitable for a wide range of targets, from individual users to large organizations across various sectors. Once deployed on a victim’s machine, the malware stealthily collects an extensive array of valuable data types, including saved passwords from browsers and FTP clients, cryptocurrency wallets, credit card information, system configurations, cookies, and even authentication tokens. Its ability to extract such a broad spectrum of data makes it especially dangerous, as it can provide attackers with the means to access bank accounts, online services, corporate networks, and personal identities without raising immediate suspicion.






